📌 Key Takeaways
- The CIA Triad is the foundational security model used in cybersecurity.
- CIA stands for Confidentiality, Integrity, and Availability.
- Every cybersecurity strategy, policy, and security framework is built around protecting these three principles.
- Modern cyberattacks often target one or more components of the CIA Triad.
- Organizations use encryption, backups, access controls, monitoring, and redundancy to protect CIA principles.
📚 Table of Contents
- What Is the CIA Triad?
- Why the CIA Triad Matters
- Confidentiality Explained
- Integrity Explained
- Availability Explained
- CIA Triad Comparison Table
- Real-World Examples
- Modern Cyber Threats
- Best Practices for Protecting the CIA Triad
- How Different Industries Use the CIA Triad
- CIA Triad in Cybersecurity Careers
- Frequently Asked Questions
- Final Summary
- References
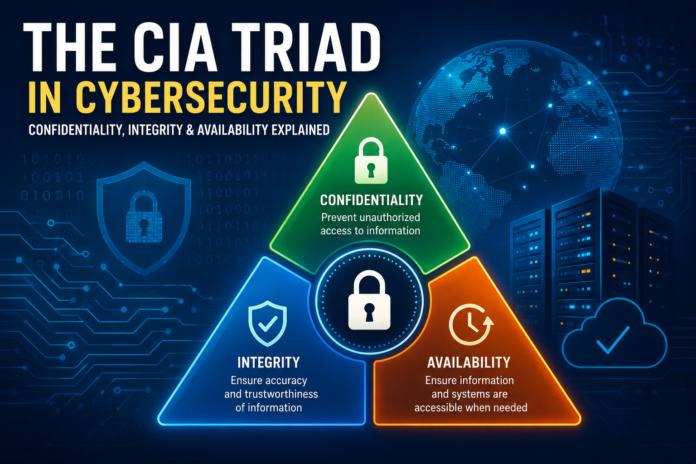
🔐 What Is the CIA Triad in Cybersecurity?
The CIA Triad is one of the most important and foundational models in cybersecurity. It represents the three core principles used to protect information systems, networks, applications, and sensitive data:
- C — Confidentiality
- I — Integrity
- A — Availability
These principles help organizations design secure systems and make security decisions that balance protection, usability, and operational continuity.
💡 Simple Definition
The CIA Triad answers three critical cybersecurity questions:
- Confidentiality: Who is allowed to see the data?
- Integrity: Can the data be trusted?
- Availability: Can authorized users access the data when needed?
The model is used across:
- Government agencies
- Banks and financial institutions
- Healthcare systems
- Cloud computing platforms
- Military systems
- Enterprise networks
- Small businesses
- Personal cybersecurity practices
🌍 Why the CIA Triad Matters
Cybersecurity is not just about stopping hackers. It is about ensuring that information remains:
- Private
- Accurate
- Accessible
If even one part of the CIA Triad fails, organizations may face:
- Data breaches
- Financial losses
- Regulatory penalties
- Operational downtime
- Reputation damage
- Legal consequences
- Loss of customer trust
⚠️ Example
A hospital may encrypt patient records (confidentiality), but if ransomware makes those records inaccessible during emergencies, the organization suffers an availability failure.
🔒 Confidentiality Explained
What Is Confidentiality?
Confidentiality ensures that sensitive information is only accessible to authorized individuals, systems, or applications.
The goal is to prevent:
- Unauthorized access
- Data leaks
- Espionage
- Identity theft
- Corporate spying
Examples of Confidential Data
- Passwords
- Credit card numbers
- Medical records
- Trade secrets
- Military intelligence
- Customer databases
- Personal identifiable information (PII)
Common Threats to Confidentiality
| Threat | Description |
|---|---|
| Phishing | Attackers trick users into revealing credentials |
| Insider Threats | Employees misuse access privileges |
| Data Breaches | Sensitive information is stolen or exposed |
| Weak Passwords | Easy-to-guess passwords allow unauthorized access |
| Misconfigured Cloud Storage | Publicly exposed databases or buckets |
How Organizations Protect Confidentiality
- Encryption
- Multi-factor authentication (MFA)
- Role-based access control (RBAC)
- Zero Trust security
- Data classification policies
- VPNs and secure communications
- Security awareness training
🔐 Security Insight
Encryption is one of the strongest methods for maintaining confidentiality. Even if attackers steal encrypted data, they cannot read it without the decryption key.
Real-World Example
A company stores customer passwords using hashing and encryption. Even if hackers access the database, the stolen passwords are difficult to decode.
🛡️ Integrity Explained
What Is Integrity?
Integrity ensures that data remains accurate, trustworthy, and unaltered unless modified by authorized individuals.
Integrity protects systems from:
- Unauthorized modification
- Corruption
- Tampering
- Fraudulent changes
- Data manipulation
Why Integrity Matters
If data cannot be trusted, organizations cannot make reliable decisions.
Imagine:
- A bank balance being altered
- A medical prescription modified
- A software update infected with malware
- A financial report manipulated
Common Threats to Integrity
| Threat | Impact |
|---|---|
| Malware | Changes or corrupts files |
| SQL Injection | Manipulates databases |
| Unauthorized Changes | Users alter sensitive records |
| Supply Chain Attacks | Compromised software updates |
| Man-in-the-Middle Attacks | Data altered during transmission |
How Integrity Is Protected
- Checksums
- Hashing algorithms
- Digital signatures
- File integrity monitoring
- Version control systems
- Database transaction controls
- Audit logging
💡 Example of Integrity Protection
When downloading software, checksums help users verify that files were not modified or infected during transmission.
Real-World Example
A hospital uses digital signatures to ensure patient records cannot be secretly altered by attackers or unauthorized employees.
⚡ Availability Explained
What Is Availability?
Availability ensures that systems, applications, and data remain accessible to authorized users whenever needed.
A system may be secure and accurate, but if users cannot access it, business operations can fail.
Common Threats to Availability
| Threat | Impact |
|---|---|
| Ransomware | Locks access to files and systems |
| DDoS Attacks | Overwhelms servers with traffic |
| Hardware Failures | System downtime and outages |
| Natural Disasters | Physical infrastructure damage |
| Power Failures | Interrupts critical operations |
How Availability Is Maintained
- Data backups
- Disaster recovery plans
- Cloud redundancy
- Load balancing
- High-availability infrastructure
- Uninterruptible power supplies (UPS)
- DDoS protection services
🔐 Security Insight
Availability is especially critical for hospitals, banks, emergency services, and cloud platforms where downtime can cause severe operational and financial damage.
Real-World Example
A cloud provider replicates customer data across multiple geographic regions to ensure services remain operational even if one data center fails.
📊 CIA Triad Comparison Table
| Principle | Primary Goal | Example Threat | Protection Methods |
|---|---|---|---|
| Confidentiality | Prevent unauthorized access | Data breach | Encryption, MFA |
| Integrity | Ensure data accuracy | Data tampering | Hashing, digital signatures |
| Availability | Ensure system accessibility | Ransomware | Backups, redundancy |
🌐 Real-World CIA Triad Examples
1. Online Banking
- Confidentiality: Customer accounts protected with encryption and MFA
- Integrity: Transaction records cannot be altered
- Availability: Banking systems remain operational 24/7
2. Healthcare Systems
- Medical records must remain private
- Patient data must be accurate
- Doctors require immediate system access during emergencies
3. E-Commerce Platforms
- Customer payment information must remain confidential
- Order data must remain accurate
- Websites must stay online during peak traffic
🚨 Modern Cyber Threats Against the CIA Triad
Ransomware
Ransomware primarily attacks availability by encrypting systems and demanding payment. However, modern ransomware groups also steal sensitive data, impacting confidentiality.
Supply Chain Attacks
Attackers compromise trusted vendors or software providers to manipulate software updates and affect integrity.
Cloud Misconfigurations
Poorly secured cloud storage buckets can expose millions of sensitive records.
Insider Threats
Employees or contractors with privileged access can intentionally or accidentally compromise all three CIA principles.
AI-Powered Cyberattacks
Artificial intelligence is increasingly used for:
- Advanced phishing attacks
- Password cracking
- Deepfake impersonation
- Automated malware
⚠️ Important Reality
Modern cyberattacks rarely target only one component of the CIA Triad. Many sophisticated attacks simultaneously affect confidentiality, integrity, and availability.
✅ Best Practices for Protecting the CIA Triad
🔒 Protecting Confidentiality
- Use strong passwords
- Enable MFA everywhere possible
- Encrypt sensitive data
- Implement least-privilege access
- Train employees against phishing
🛡️ Protecting Integrity
- Use hashing and digital signatures
- Monitor for unauthorized changes
- Apply software patches regularly
- Implement secure coding practices
- Use audit logs
⚡ Protecting Availability
- Maintain offline backups
- Use cloud redundancy
- Create disaster recovery plans
- Deploy DDoS protection
- Monitor infrastructure continuously
📋 CIA Triad Security Checklist
✔ Confidentiality Checklist
- ☐ Enable multi-factor authentication
- ☐ Encrypt sensitive data
- ☐ Restrict user permissions
- ☐ Conduct employee security training
- ☐ Monitor for suspicious access
✔ Integrity Checklist
- ☐ Verify file integrity regularly
- ☐ Use secure update mechanisms
- ☐ Maintain audit trails
- ☐ Implement change management
- ☐ Use digital signatures
✔ Availability Checklist
- ☐ Maintain secure backups
- ☐ Test disaster recovery plans
- ☐ Use redundant systems
- ☐ Monitor uptime continuously
- ☐ Protect against DDoS attacks
🏢 How Different Industries Use the CIA Triad
| Industry | CIA Focus | Examples |
|---|---|---|
| Healthcare | Confidentiality | Patient record privacy |
| Banking | Integrity | Accurate transactions |
| Cloud Services | Availability | Continuous uptime |
| Government | All three | National security systems |
🎓 CIA Triad in Cybersecurity Careers
The CIA Triad is taught in nearly every cybersecurity certification and training program.
Professionals using CIA principles include:
- Security Analysts
- Network Engineers
- Penetration Testers
- Cloud Security Architects
- Risk Analysts
- Compliance Officers
- Incident Responders
Popular Certifications Covering the CIA Triad
- CompTIA Security+
- CISSP
- CEH
- CISM
- CCSP
- Google Cybersecurity Certificate
📈 Cybersecurity Facts & Statistics
- 🌍 Cybercrime damages are projected to exceed trillions of dollars annually worldwide.
- 🔐 Human error remains one of the leading causes of data breaches.
- ☁ Cloud misconfigurations continue to expose millions of sensitive records every year.
- 💣 Ransomware attacks increasingly target critical infrastructure and healthcare systems.
- 📱 Multi-factor authentication significantly reduces account compromise risks.
❓ Frequently Asked Questions (FAQ)
What does CIA stand for in cybersecurity?
CIA stands for Confidentiality, Integrity, and Availability.
Why is the CIA Triad important?
It provides the foundational framework used to secure data, systems, and networks against cyber threats.
Which component of the CIA Triad is most important?
All three are critical. Different industries prioritize them differently depending on operational requirements and risks.
How does ransomware affect the CIA Triad?
Ransomware primarily impacts availability, but modern attacks also steal data and threaten confidentiality.
What is an example of confidentiality?
Encrypting customer credit card information to prevent unauthorized access.
What is an example of integrity?
Using digital signatures to verify that software updates were not modified.
What is an example of availability?
Maintaining backups and redundant servers to keep services online during outages.
Is the CIA Triad still relevant today?
Yes. Despite evolving technologies and threats, the CIA Triad remains the core foundation of cybersecurity frameworks worldwide.
🧾 Final Summary
The CIA Triad remains the backbone of modern cybersecurity.
By protecting:
- Confidentiality → keeping data private
- Integrity → ensuring data accuracy
- Availability → maintaining reliable access
Organizations can reduce cyber risk, improve resilience, and build trust with users and customers.
Whether you are:
- A student learning cybersecurity
- A business owner protecting customer data
- An IT professional securing infrastructure
- A general user improving online safety
Understanding the CIA Triad is essential for navigating today’s digital world safely and effectively.
✅ Final Security Tip
Cybersecurity is not achieved through a single tool or technology. True security comes from balancing confidentiality, integrity, and availability together.
📚 References & Authoritative Sources
- National Institute of Standards and Technology (NIST)
- Cybersecurity and Infrastructure Security Agency (CISA)
- OWASP Foundation
- Microsoft Security Documentation
- Google Security Best Practices
- IBM Security Resources
- Cloud Security Alliance (CSA)
- CompTIA Security+ Study Materials